I need a bit of help
I am new to pc and When trying to play certain games it tells me to update bios, when i go to the hp site it doesn't show my os. how am i supposed to update bios?
Travel router on RPi5 with 4G
Hi everyone, im making a travel router for low connection places like in valleys inbetween mountains and similar, any help? Im using the Raspberry Pi 5, sim7600G-H and a pijuice.
My questions below
1. Does it matter if i put the 4g hat before the pijuice on the RPi5 or not?
...
help with hosting a mc server
hello i want help hosting a mc server using termux anyone?
i have got the ssh key and stuff...
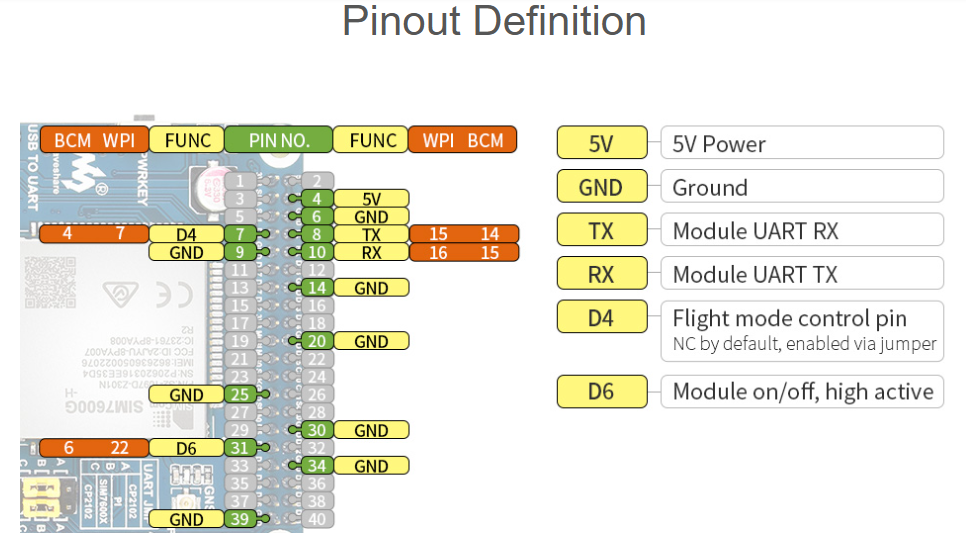
Raspberry Pi 5 soft shutdown to HAT through GPIO pin 31
Hello, im making a cellular hotspot using a raspberry pi 5, but i noticed that i have to either shut the cellular HAT off manually, or i have to somehow send an off signal to the GPIO 31 pin, i found that adding "dtoverlay=gpio-poweroff,gpiopin=31,active_high" to the "/boot/firmware/config.txt" file is supposed to work, can anybody verify this. I havent ordered the raspberry pi 5 and want to verify this with somone before committing to it.
Raspberry Pi 5 with SIM7600G-H 4G HAT, using 2 IPEX1 to SMA cables to connect 2 antennas im mounting on the custom enclosure im making,
with the AWUS036AXML Alfa adapter as an access point....
help with hosting a mc server
hello i want help hosting a mc server using termux anyone?
i have got the ssh key and stuff...
Backup multiple PCs
hi guys - i was wondering, is there a relatively painless way for me to create a backup of all the data on my 4 PCs and 1 NAS? ideally i'd like to create one portable physical storage device (like a usb hdd). some PCs have multiple operating systems on them. i do not need to replicate them exactly, i just care about preserving all the data. my first idea was to get a 20tb usb hdd, plug it and a live os usb into each device and copy all the data.
I need help
so basically I was trying too download an executor and then like most of my files turned into the avg antivirus logo what do I do to get rid of it It had a lot of info in there and idk the 48 digit key
Onionshare persistance in Tails OS
I recently started trying Tails OS, but im seeing an issue with using persistance in OnionShare. I am trying to save a onionshare chat server than i can save so it keeps the same link when i reboot and relaunch it, but with dotfiles, it fails to launch because the onionshare.json is glitching. What do i do to make it so persistance works, since onionshare.json has a variable linked to persistance that breaks if i only save one of them, but with both it fails to launch. Please help or give me so...
Solution:
Appears nobody knows about tails os, i never got an answer so i will just close this and set it up on onionshare on another device
Ethernet Problem
Please I need someone's help please my ethernet cable doesn't work please I disconnect it and everything and it still doesn't go if someone can help me I would thank you please it's very urgent I've restarted the network I've done everything I've cleaned the dns cache and it still doesn't work.
phone problem
Hello, I have a problem with my phone. For a few months now it has been bugging and I would like to know how to stop it. Thank you.
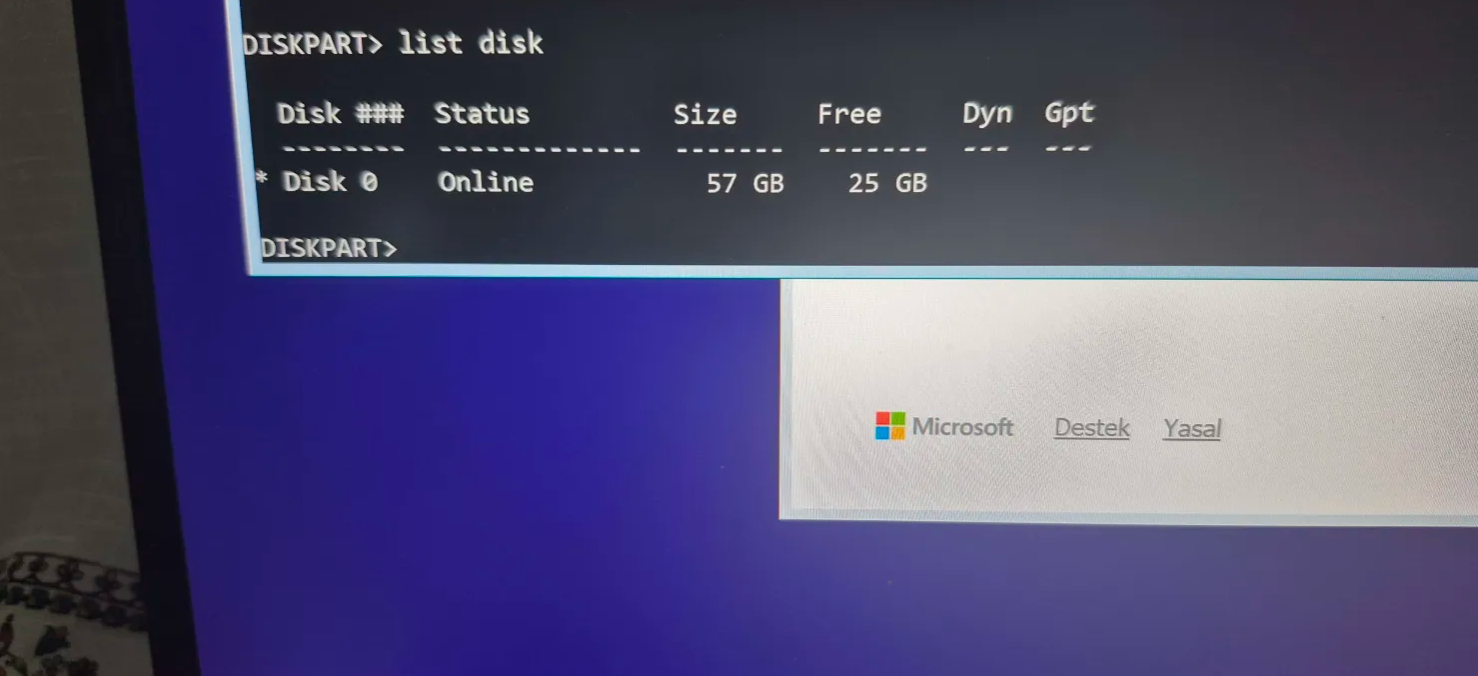
Hello Need help with diskpart
I was normally doing a format but I got bitlocker and then cleared it after I cleared it I wasnt able to see my ssd at diskpart could really usa a help pls
MacOS Target Disk Mode cable recommendations
Hi all, I have a Mac that I want to connect a Raspberry Pi Model 3 to via Target Disk Mode.
I want to access the drive from the Pi to help a family member recover a forgotten FileVault key.
The Pi has USB-A ports, while the Mac has USB-A, USB-B, and Thunderbolt (either version 1 or 2 I'm not sure) ports.
What's the cheapest way to connect the two for TDM? Ideally I won't spend too much money on cables, but I know that Apple stuff is marked up by a lot....
Hii
Helloo, i actually have free time for learning a language, did i continue to learn html css or i start python or js or other (im a newbie on html css)
Help me decode this string pls
hello, can anyone help me decode this string or help me figure out what exactly has been done on this string:
NOT BEEN ABLE TO FIND THIS FOR DAYS NOW:
3C=%^g*^@0V3<=x;@Eha-T/FDog>VpU,7yHrmmaJ9dDX(C!W2xFOElU$(X=d%sWp6J\a^n4scFD]mm...
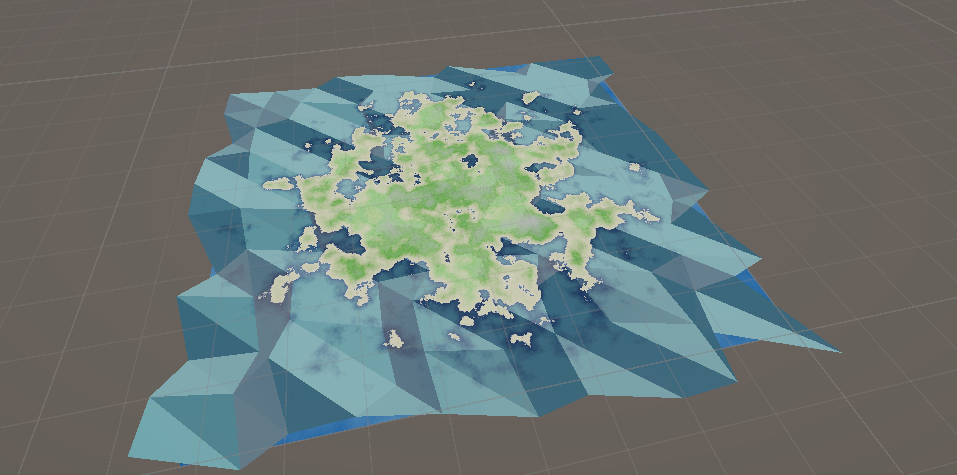
Unity Low-poly water tiling
Hello, I have made water texture following this video: https://youtu.be/78WCzTVmc28?si=98FFRm2NOKs0ckua
What i need it to make the texture tilable so the texture size is the same as I scale up the size of the plane.
I attached picture so you can see how the water is rn.. ¨...
Need Cybersecurity Course Advice
Hey, I’m interested in pursuing cybersecurity. Can you recommend any courses I should consider?
Ubuntu not booting
As mentioned in a previous post, I had trouble deciding what new linux os to use. I decided on Ubuntu. Anyway, I used Rufus to create a bootable usb drive. I went into the startup menu to select what to boot from, but when I selected my usb drive it went directly to windows again. I tried rearranging the boot order from the bios, but it kept restarting the process. Any ideas?
Solution:
Nvm got it to work. I just had to install an iso that fully supported bios.